Most RPC conversations start with uptime. Is the provider online? Is the endpoint responding? Are requests being served?
Those questions matter. But they are not enough.
For critical blockchain applications, the bigger question is not only whether your RPC provider responds. The bigger question is whether the response can be trusted.
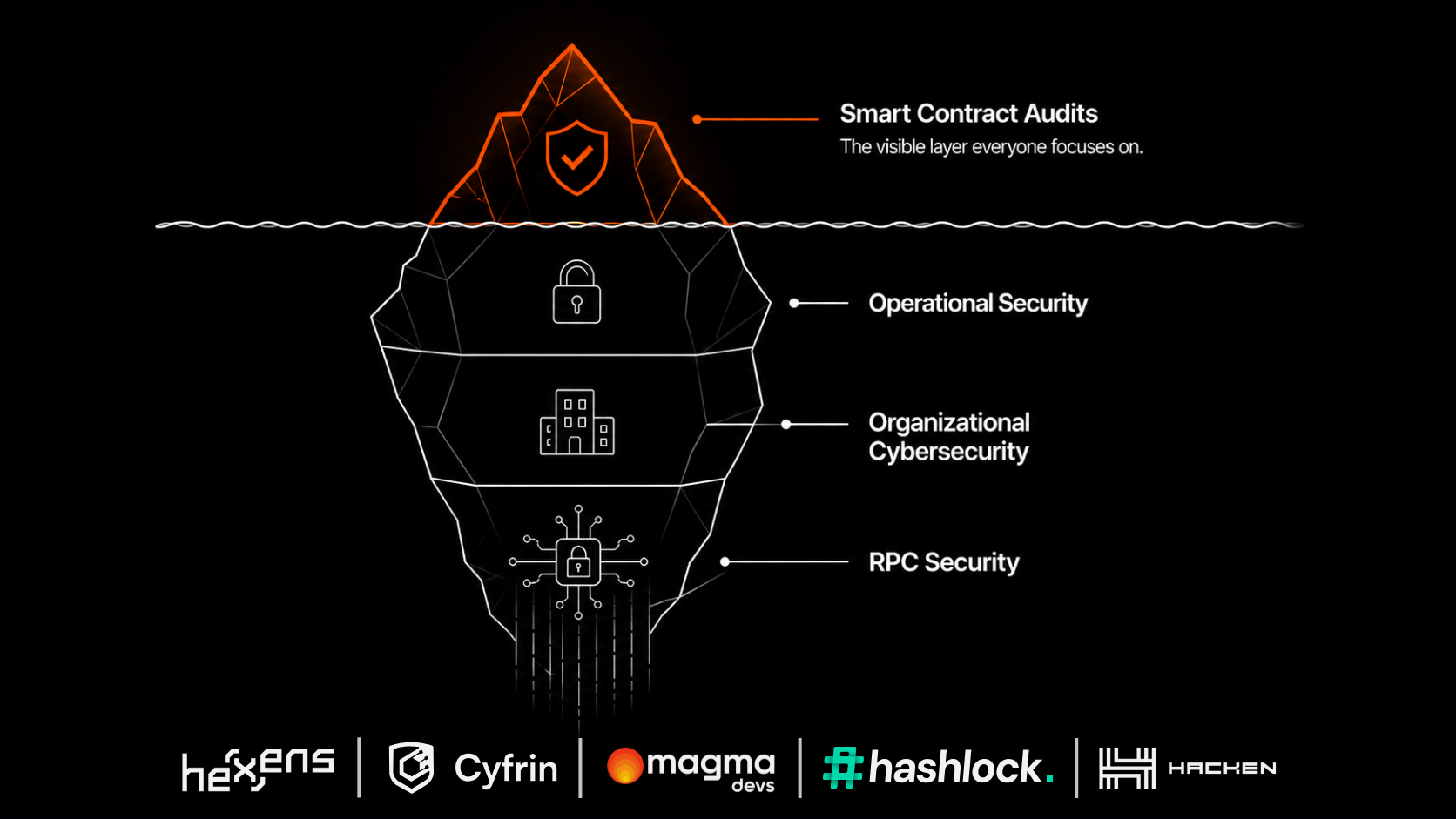
That is where RPC security begins.
The old view: RPC is about access
Traditionally, teams treated RPC as an access layer. The application needs blockchain data, so it sends requests to an RPC provider. As long as the provider responds, everything looks fine.
This view is too narrow. It assumes that the main risk is downtime. But blockchain applications do not only need data. They need reliable data.
A fast response is not useful if it is stale, inconsistent, incomplete, or wrong.
The real risk: bad data can look normal
A failed RPC request is easy to detect. The request times out. The endpoint is unavailable. The system throws an error.
Bad data is harder. The response may look valid. The API may return a normal result. The application may continue operating as if nothing is wrong. But under the surface, the system may be relying on information that should not be trusted.
That can create serious issues for exchanges, custodians, wallets, bridges, DeFi protocols, analytics platforms, and security tools.
Examples of RPC data risk
Stale data. The provider responds, but the data is behind the chain. Your application may think a transaction is not confirmed yet, or may show an outdated balance.
Inconsistent data. Different providers return different answers for the same request. Without validation, your system may not know which answer to trust.
Partial failure. Some chains, methods, or regions may be affected while others work normally. A generic uptime check may miss the issue.
Incorrect transaction state. Your app may misread whether a transaction succeeded, failed, or is still pending. For user-facing financial products, this can create confusion, support load, and operational risk.
Manipulated or compromised responses. In more severe scenarios, relying on one source creates exposure if that source is compromised or manipulated. Even if this is rare, the impact can be high enough that serious teams should not ignore it.
Why failover alone is not enough
Many teams think the answer is simple: use a backup provider. That is a good start, but it is not enough.
Basic failover usually answers one question: if provider A is down, can we move to provider B?
But RPC security requires more questions:
- What if provider A is online but slow?
- What if provider A returns stale data?
- What if providers disagree?
- What if only one method or one chain is affected?
- What if the backup provider has different behavior?
- What if switching manually takes too long?
A backup provider is useful. But without smart routing, validation, and observability, you may still be operating blindly.
What RPC validation means
RPC validation means your system does not automatically trust one response from one provider. Instead, it can compare responses across multiple providers or sources and detect when something does not look right.
A simple example: your system asks three providers for the latest block number. If all three agree, confidence is higher. If one provider returns a different result, the system can flag it, route around it, or apply a defined rule.
This is sometimes called a quorum model. In plain English: do not rely on one witness when the decision matters.
Availability protects access. Validation protects trust.
Availability answers: can we reach blockchain data? Validation answers: can we trust the data we received?
Both matter. If your application is only optimized for availability, it may still be exposed to bad data. If your application validates data but has no failover, it may still break when access fails. Enterprise-grade RPC infrastructure needs both.
Who should care most?
RPC security matters most for teams where wrong blockchain data can create financial, operational, or reputational damage. That includes exchanges, custodians, wallets, bridges, DeFi protocols, blockchain security companies, analytics platforms, institutional blockchain products, and any application handling high-value transactions or sensitive user flows.
For these teams, RPC is not just a backend detail. It is part of the trust architecture.
Where Smart Router fits
Magma's Smart Router is built to help teams move beyond basic RPC access. It provides a smarter layer between the application and RPC providers, helping teams route requests, fail over across providers, and validate responses where needed.
Instead of asking, "Is our RPC provider online?" teams can ask better questions:
- Which provider is best for this request?
- Are providers returning consistent answers?
- Is one provider behaving abnormally?
- Can we fail over before users are impacted?
- Do we have visibility into the RPC layer?
That is the shift from RPC access to RPC security.
The bottom line
RPC uptime is important. But uptime alone does not make your infrastructure secure. If your application blindly trusts one provider, you still have a major risk.
For critical blockchain operations, the standard should be higher: multiple providers, smart routing, response validation, clear observability. Because in blockchain infrastructure, the cost of trusting the wrong data can be much higher than the cost of no data at all.
How exposed is your RPC stack?
Take the 2-minute Secure RPC Assessment and get a personalized risk report.
Run the assessment