Many serious blockchain teams eventually reach the same conclusion: relying on one RPC provider is too risky.
The natural next thought is: "We can build our own routing layer."
That is not a bad instinct. Strong engineering teams like to control critical infrastructure. They do not want to depend blindly on vendors. They want flexibility, visibility, and resilience.
But RPC routing looks simpler than it really is. Basic failover is easy to build. Enterprise-grade RPC resilience is not.
What teams usually build first
The first version usually looks something like this:
- Use provider A as the default
- If provider A fails, switch to provider B
- Add basic retries
- Add timeout logic
- Add a few alerts
This can be useful. It is better than having no backup at all. But it is not a full routing layer. It is usually a thin fallback script around a few providers. That may work for low-risk use cases. It is not enough for critical blockchain operations.
Why RPC routing becomes complex
The complexity appears after the first incident, the first scale problem, or the first customer-facing failure. Suddenly the team realizes that routing is not just about switching from provider A to provider B. It is about making the right decision across providers, chains, methods, traffic patterns, and failure types.
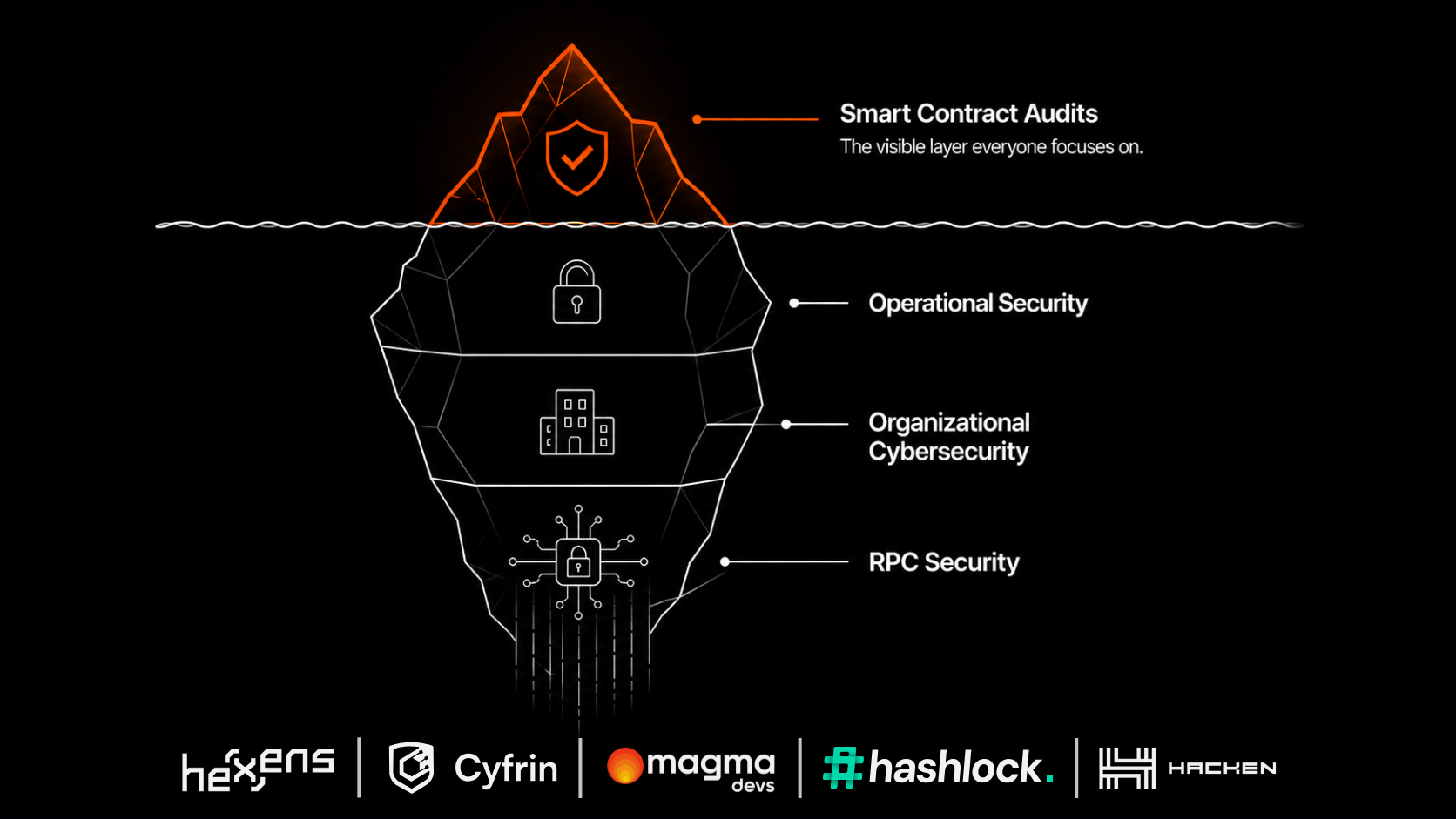
Hidden challenge 1: not all failures are obvious
A provider can be online and still be unhealthy. It may be slow. It may return stale data. It may fail only for a specific method. It may have issues in one region. It may behave differently on one chain than another.
A basic uptime check will not catch all of this. Your system needs deeper health logic.
Hidden challenge 2: latency changes constantly
The fastest provider today may not be the fastest provider tomorrow. Performance can change by chain, geography, time of day, and request type.
If your routing logic does not measure and adapt, you may be sending traffic to the wrong place. For user-facing applications, latency is not an internal metric. It becomes user experience.
Hidden challenge 3: providers behave differently
RPC providers are not identical. They may differ in supported chains, supported methods, rate limits, archive access, error formats, data freshness, regional performance, pricing models, and SLA terms.
A routing layer needs to normalize these differences so the application does not become messy and provider-specific.
Hidden challenge 4: failover needs to be safe
Switching providers sounds simple. But a bad failover can create its own problems. The backup provider may be slower. The backup may not support the same method. The backup may return inconsistent data. The switch may happen too late, or too often. The team may not understand why traffic moved.
Failover without visibility creates a new kind of operational risk.
Hidden challenge 5: validation is harder than fallback
Failover protects you when a provider is unavailable. Validation protects you when a provider returns questionable data. That is a harder problem.
It requires comparing responses, defining trust rules, detecting disagreement, and deciding how the system should behave when providers do not align. This is where many internal builds stop too early. They solve access redundancy, but not data trust.
Hidden challenge 6: someone has to maintain it
The biggest mistake in build vs. buy discussions is underestimating maintenance. An internal routing layer is not a one-time project. It needs ongoing work: adding providers, removing bad providers, updating chain support, monitoring provider behavior, handling new edge cases, maintaining dashboards, tuning routing logic, debugging incidents, supporting internal teams, and preparing for customer audits or enterprise reviews.
The real cost is not only the initial build. The real cost is the engineering attention it consumes forever.
When building internally makes sense
Building may make sense if RPC routing is core to your product, you have a dedicated infra team, and you are willing to own the full operational burden. It may also make sense if your needs are extremely custom and no external product can support them.
But teams should be honest. If the internal solution is not deeply maintained, monitored, tested, and owned, it can become a false sense of security.
When buying makes more sense
Buying makes more sense when your team wants enterprise-grade RPC resilience without turning it into a permanent internal platform project. This is especially true if your company cares about high availability, provider redundancy, fast failover, response validation, observability, multi-chain support, SLA-backed infrastructure, reduced vendor dependency, and reduced engineering distraction.
In that case, the question is not "Can we build something?" Of course you can. The better question is:
Should your best engineers spend their time building and maintaining RPC routing, or should they focus on your core product?
Where Smart Router fits
Magma's Smart Router is designed for teams that need a stronger RPC layer but do not want to build and operate the entire system internally. It provides routing, failover, validation, and observability across multiple providers.
The goal is not to replace your engineering team. The goal is to give your engineering team a more reliable foundation, so they do not need to reinvent the same infrastructure layer themselves.
The build vs. buy test
Before deciding to build internally, ask these questions:
- Who owns this system after the first version ships?
- How will we detect stale or inconsistent data?
- How will we decide which provider gets each request?
- How will we handle provider-specific behavior?
- How will we monitor performance by provider and chain?
- How will we test failover before an incident?
- How will we explain provider decisions during an incident?
- How much engineering time will this consume over the next 12 months?
- Is this infrastructure layer a strategic differentiator for us?
- What is the cost if our internal solution fails during a critical moment?
If you do not have clear answers, building may be more expensive than it looks.
The bottom line
Basic RPC failover is easy. Reliable, observable, validated, enterprise-grade RPC routing is much harder. Do not confuse the first with the second.
If your application is critical, your RPC layer needs to be treated as critical infrastructure. And critical infrastructure should not depend on improvised fallback logic.
How exposed is your RPC stack?
Take the 2-minute Secure RPC Assessment and get a personalized risk report.
Run the assessment